Real Output From a Real Scan
These are actual screenshots from a completed scan. Not mockups.
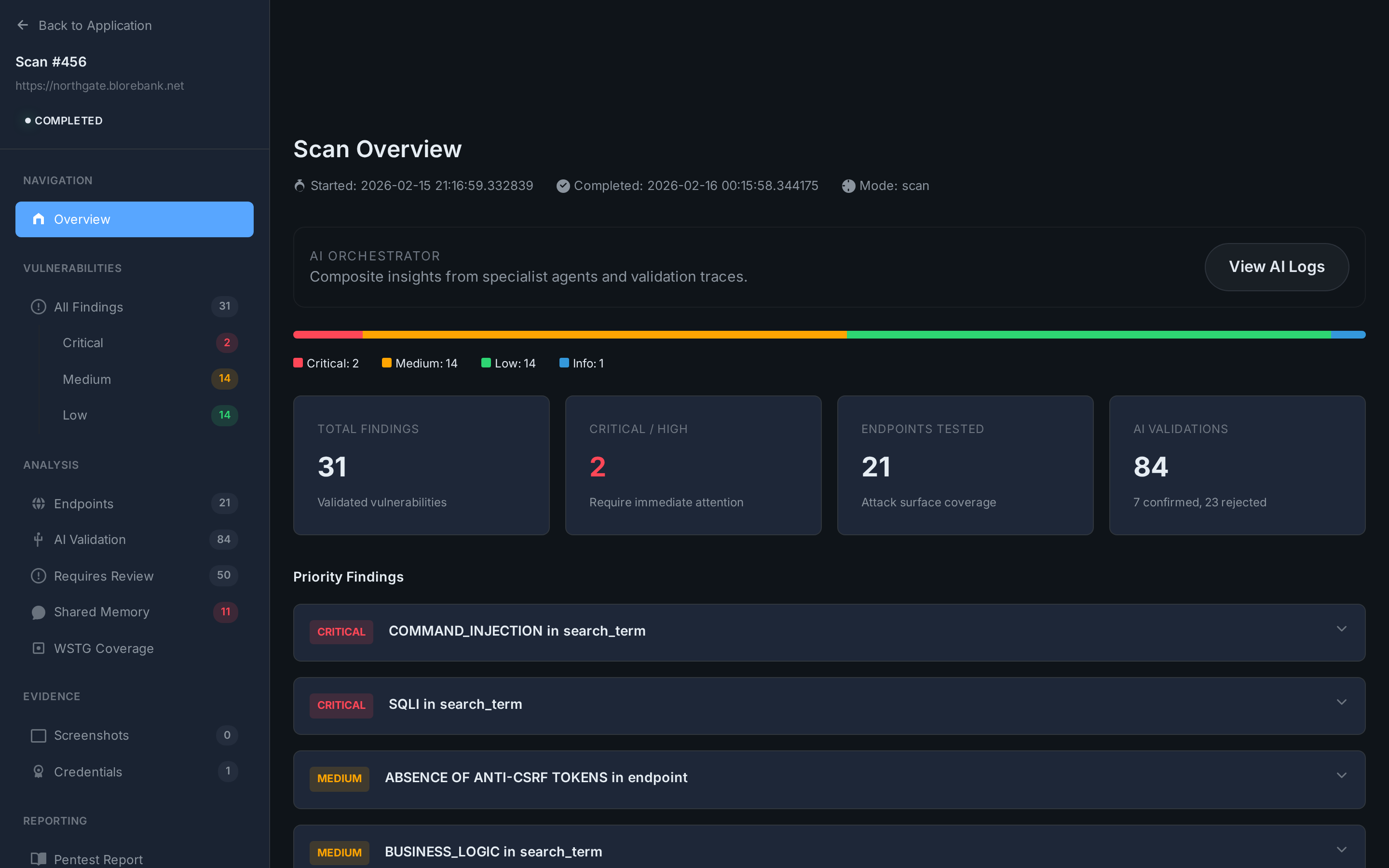
Scan Overview
31 validated findings, 84 AI validation runs, severity breakdown with priority findings. One-click access to findings, endpoints, AI traces, and WSTG coverage.
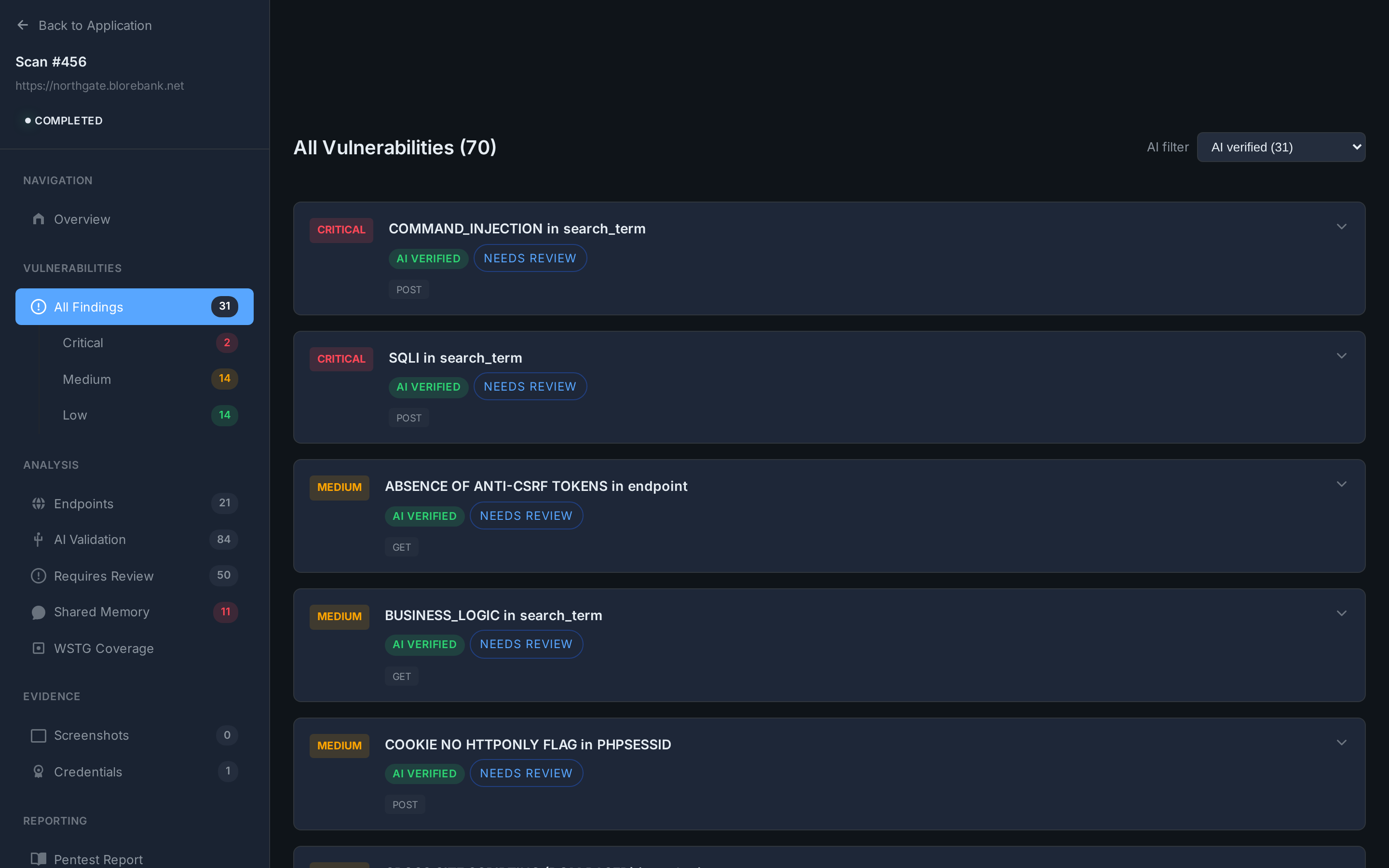
Findings List
Every finding tagged with severity, AI VERIFIED status, and HTTP method. Filter by severity or validation state.
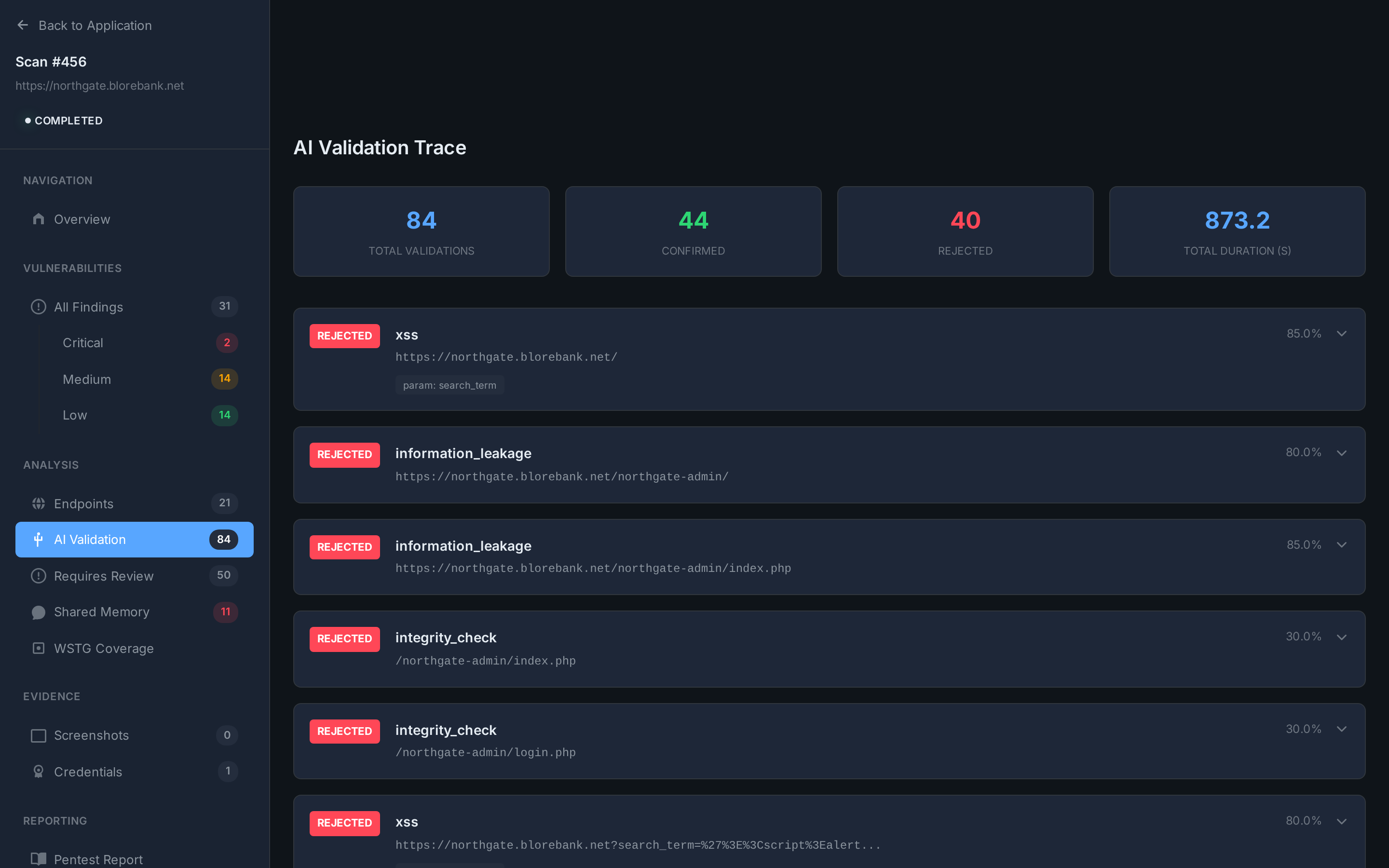
AI Validation Trace
84 total validations. 44 confirmed, 40 rejected. Every decision logged with confidence score and reasoning chain.
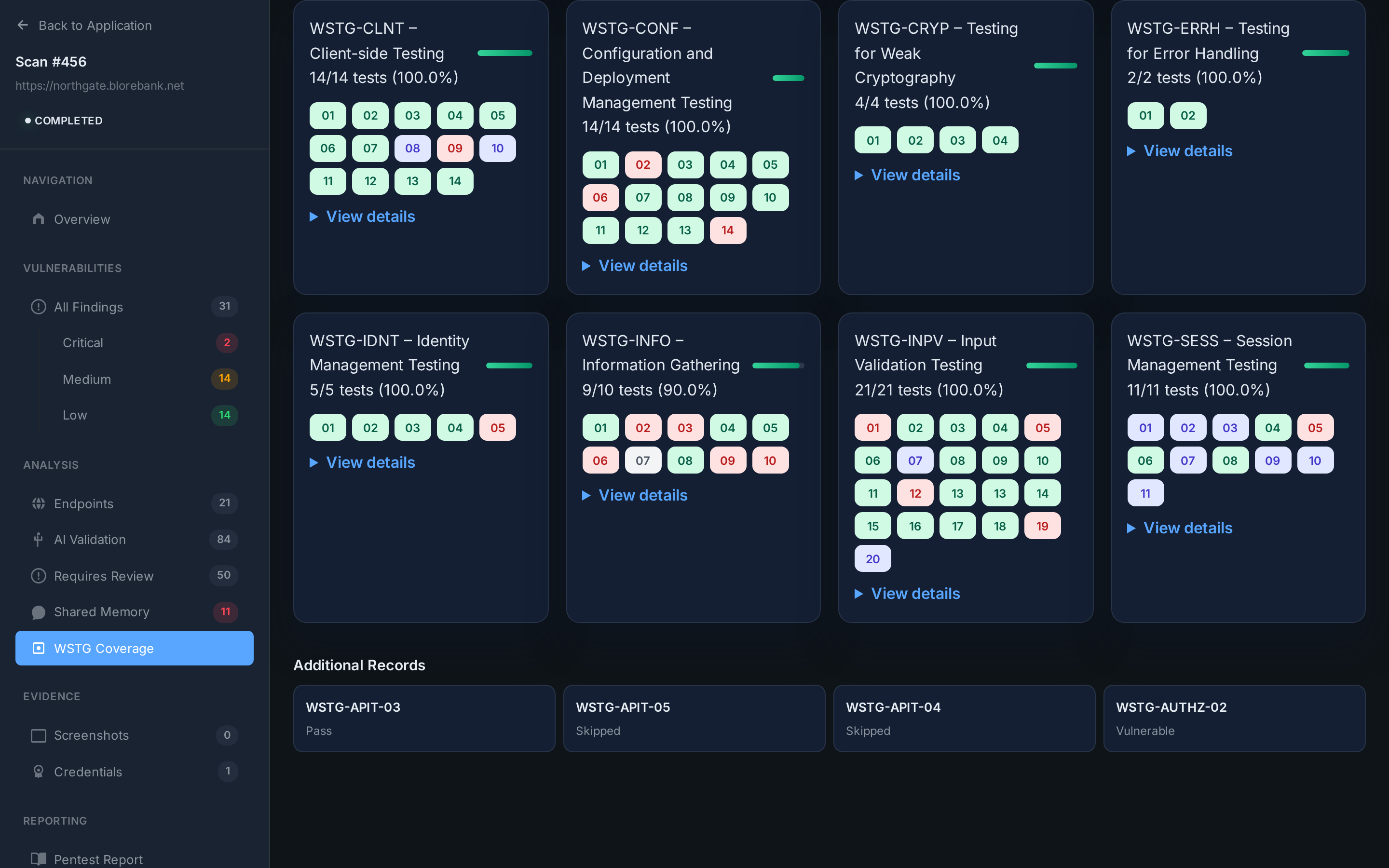
WSTG Coverage Matrix
Every WSTG test ID tracked across 12 categories. Green = tested. Coverage percentage per category. Gap analysis built in.
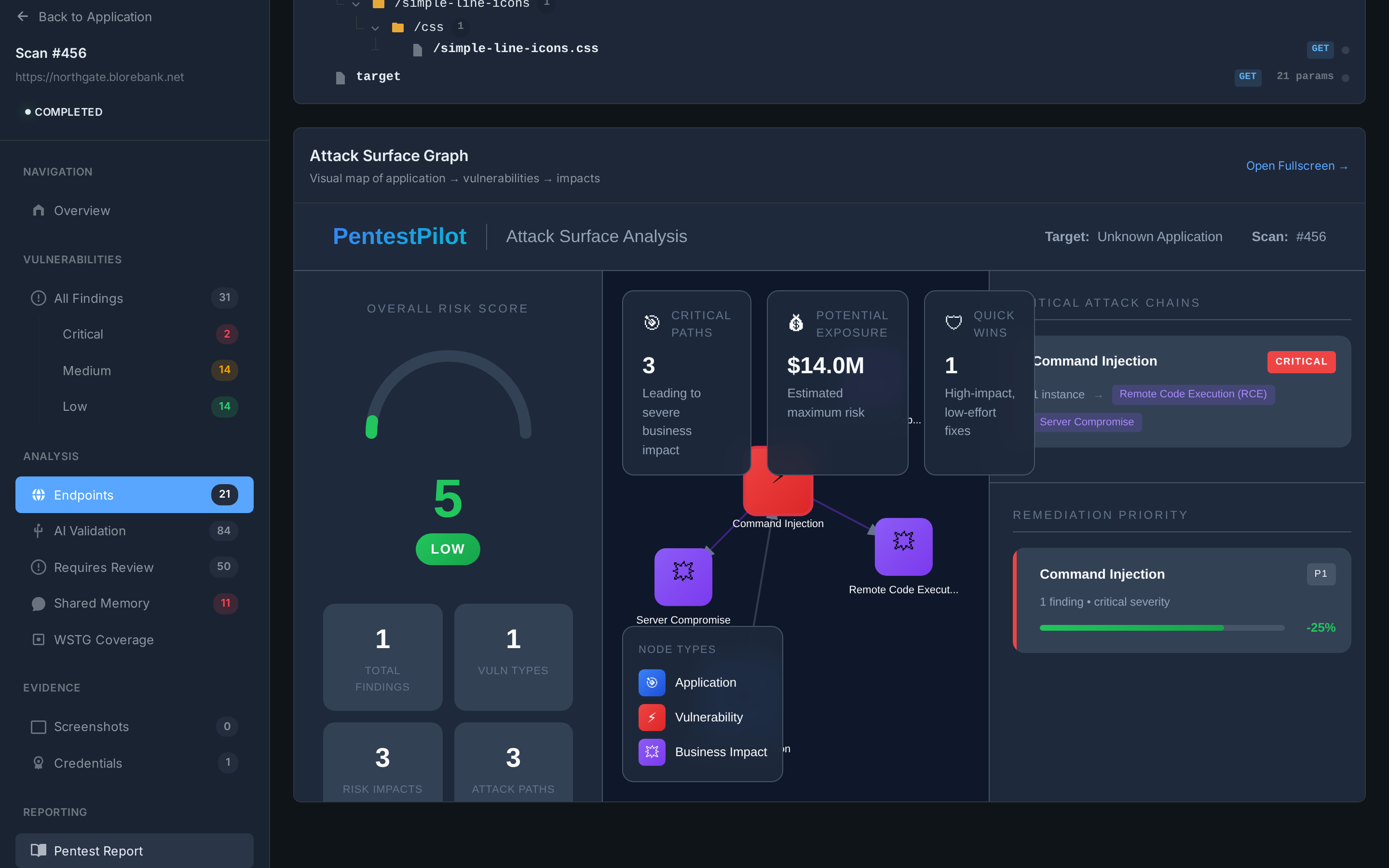
Attack Surface Graph
Visual exploit chain mapping. Critical attack paths, potential exposure scoring, remediation priority. Interactive full-screen view.
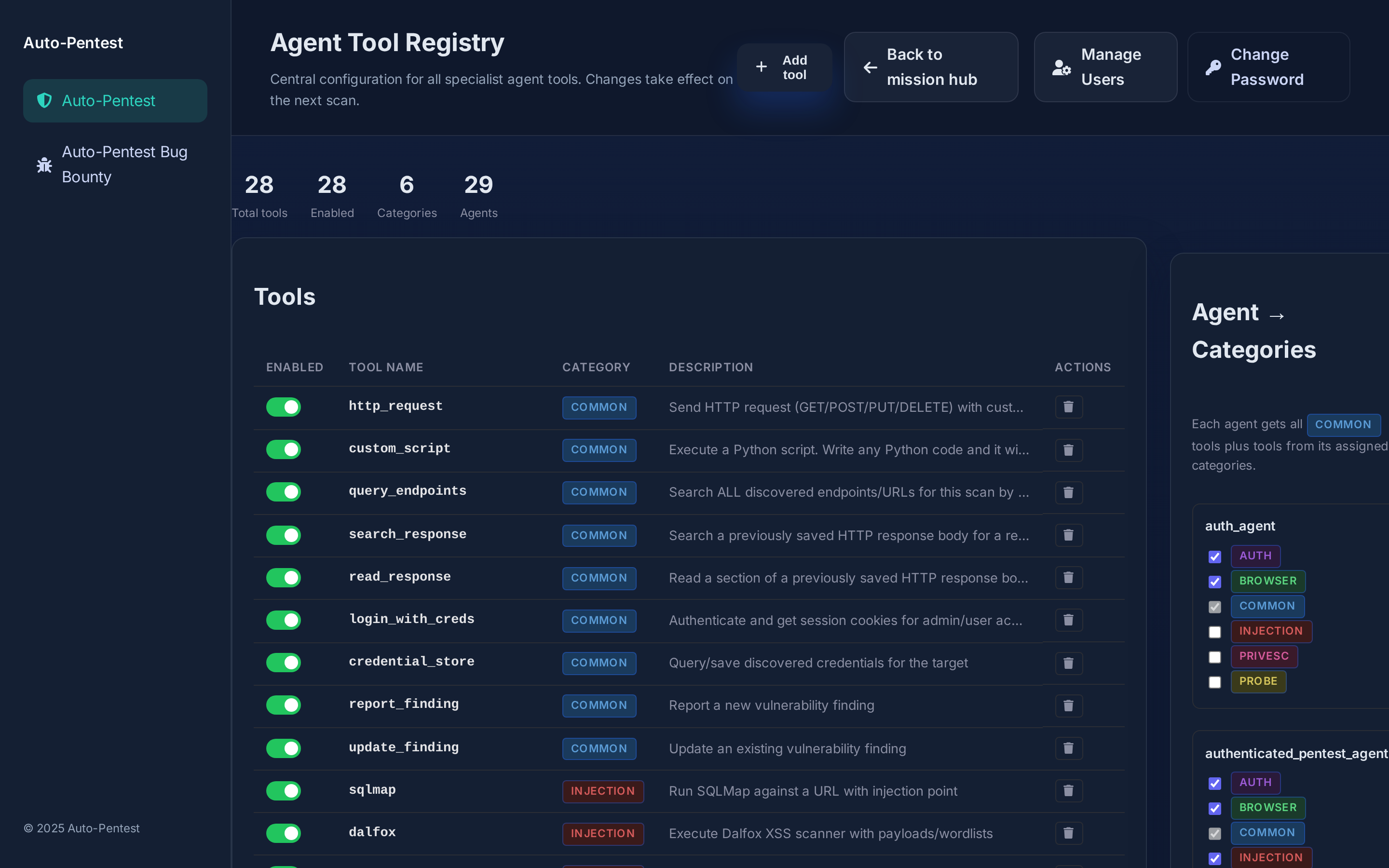
Agent Tool Registry
28 tools across 6 categories. Each specialist agent gets tools from its assigned categories. Toggle tools on/off per scan.